Risk Management in Media to Disciple Making Movements (M2DMM)
Risk management is not simple, not a one-time event or decision, but it is essential. It also is wholistic, choices you make (or fail to make) in one area affect the whole. We want to equip you by sharing some of the best practices we have picked up along the way. May we courageously push back against fear while yielding to wisdom, and may God give us the insight to discern between the two.
If you would like to add something you have learned, feel free to leave a comment at the bottom.
Add Protection to your Devices
Make it part of your partnership agreements that M2DMM members must secure their devices (i.e., laptop, desktop, tablet, hard drive, mobile phone)

➤ Turn on screen lock (e.g., if your device is not active for 5 minutes, it will lock and require the password).
➤ Create strong passwords/biometrics for accessing devices.
➤ Encrypt devices.
➤ Install an Antivirus application.
➤ Always install the latest updates.
➤ Avoid turning on autofill.
➤ Do not stay logged into accounts.
➤ Use a VPN for work.
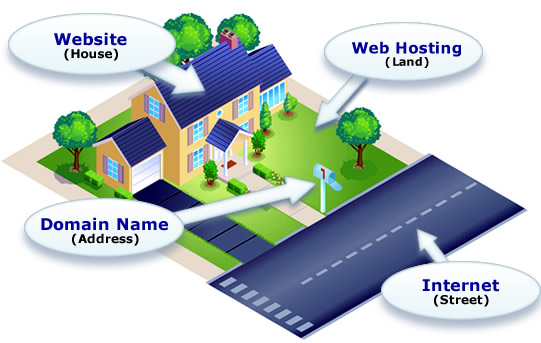
Secure Sockets Layer (SSL) or HTTPS
If a site doesn’t have an SSL Certificate, then it’s vital that it’s setup. SSL is used to protect sensitive information sent across the Internet. It is encrypted so that the intended recipient is the only one who can access it. SSL is vital for protection against hackers.
Again, if you have created a website, whether it is a prayer website, an evangelistic site, or a Disciple.Tools instance, you need to set up SSL.
If a site has an SSL Certificate, the URL will begin with https://. If it does not have SSL, it will begin with http://.

The easiest way to set up SSL is through your hosting service. Google your hosting service’s name and how to set up SSL, and you should be able to find instructions on how to do this.
Examples of hosting sites and their SSL setup guides:
Secure Backups
Secure backups are crucial in risk management. You must have backups to your backups for your all websites including your Disciple.Tools instance. Do this for your personal devices as well!
If you have secure backups in place, then you will not have to worry about website crashes, accidental deletions, and other major mistakes.
Website Backups

Primary Storage: Setup automatic backups weekly to a secure storage location. We recommend Amazon S3.

Secondary and Tertiary Storage: Occasionally and especially after significant upgrades, make copies of those backups in a couple of other secure storage locations (i.e., Google Drive and/or encrypted and password protected external hard drive)
If you are using WordPress, consider these backup plugins:

We recommend and use UpraftPlus for our backups. The free version does not backup Disciple.Tools data, so to use this plugin, you must pay for the premium account.

We’ve also tested BackWPup. This plugin is free but more challenging to set up.
Limited Access
The more access you give to accounts, the higher the risk. Not everyone needs to have the Admin role of a website. An Admin can do just anything to a site. Learn the different roles for your site and give them out according to the person’s responsibilities.
If there is a breach, you want the least amount of information to be available. Do not give access to valuable accounts to people who do not maintain cybersecurity best practices.
Apply this principle to websites, social media accounts, password managers, email marketing services (i.e., Mailchimp), etc.
If you are using a WordPress site, you can change a user’s role and permission settings.

Secure Passwords
First off, DON’T SHARE PASSWORDS with others. If you have to for whatever reason, change your password afterward.
Second, it is VITAL that everyone who is part of your M2DMM team uses secure passwords.
The more a person has access to, the more intentional they will need to be about having a different secure password for EVERY account.

It is nearly impossible to remember these passwords, and it is not wise to write down your passwords in a notebook or save them directly to your computer. Consider using a password manager like 1Password.

Make sure your email has been signed up to Have I been pwnded?. This site will notify you when your email appears in a hacked and leaked database online. If this happens, change your password immediately.
2-Step Verification
Whenever possible, use 2-step verification. This will offer your digital accounts the most protection from hackers. However, it is imperative that you securely save backup codes for every account that you use it with. This is in case you accidentally lose the device that you use for 2-step verification.

Secure Email
You want an email service that stays up to date on the latest security features. Also, do not use your personal name or identifying details in your user information.

Gmail is one of the leading email services for email security. If you use it, it blends in and does not make it seem like you are trying to be secure.

Protonmail is newer and currently has active updates. If you are using it, it is obvious that you are trying to use a secure email and it does not blend in with other emails.
Virtual Private Networks (VPNs)
VPNs are something to consider whenever you are making a risk management plan. If you live in a high-risk location, a VPN will be another layer of protection for M2DMM work. If you do not, it may or may not be necessary.
Do not use a VPN when accessing Facebook, as this may cause Facebook to shut down your advertising account.
VPNs change the IP address of a computer and give your data an extra layer of protection. You will want a VPN if you don’t want the local government or Internet Service Provider to see which websites you are visiting.
Keep in mind, VPNs slow down connection speed. They can interfere with services and websites that don’t like proxies, and this might cause your account to be flagged.
 VPN Resources
VPN Resources
- Check out The Best VPN Service 2019 by Tech Radar
- It is easy to set up a VPN in such a way that it is not actually protecting you from surveillance. To check if your VPN is working properly, visit https://ipleak.net/ or https://www.wizcase.com/tools/whats-my-ip/.
Digital Hero
When you set up digital accounts, they will ask for personal information such as name, address, phone numbers, credit card information, etc.
To add an additional layer of security, consider recruiting a Digital Hero to your team. A Digital Hero volunteers their identity to set up the digital accounts.
A Digital Hero represents a legal entity like a business, non-profit or organization to set up a Meta Business Account in the name of the legal entity. Meta is the parent company of Facebook and Instagram.
They are someone not living in country who is able to protect the ministry from localized security threats (i.e. hackers, hostile groups or governments, etc).
Encrypted Hard Drives
Like VPNs and Digital Heros, having fully-encrypted hard drives is a risk management best practice for high-risk fields.
Be sure to fully encrypt the hard drives on all of your devices (i.e., laptop, desktop, tablet, external hard drive, mobile phone)
iPhones and iPads
As long as you have a passcode set on your iOS device, it is encrypted.
Laptops
Whoever has physical access to your computer doesn’t need your password to see the files. They can simply remove the hard drive and insert it into another machine to read the files. The only thing that can stop this from working is full-disk encryption. Don’t forget your password, as you can’t read the disk without it.
OS X 10.11 or later:

1. Click the Apple menu, and then System Preferences.
2. Click Security & Privacy.
3. Open the FileVault tab.
4. FileVault is the name of OS X’s full-disk encryption feature, and it must be enabled.
Windows 10:
Newer Windows 10 laptops automatically have full-disk encryption enabled if you sign in with a Microsoft account.
To check that full-disk encryption is enabled:
1. Open the Settings app
2. Navigate to System > About
3. Look for the “Device Encryption” setting at the bottom of the About panel.
Note: If you don’t have a section entitled “Device Encryption,” then look for the setting entitled “BitLocker Settings.”
4. Click on it, and check that every drive is marked “BitLocker on.”
5. If you click on it and nothing happens, you don’t have encryption enabled, and you need to enable it.

External Hard Drives
If you lose your external hard disk, anyone can take and read its contents. The only thing that can stop this from happening is full-disk encryption. This applies to USB sticks too, and any storage devices. Don’t forget your password, as you can’t read the disk without it.
OS X 10.11 or later:
Open Finder, right-click on the drive, and choose “Get Info.” The line marked “Format” should say “encrypted,” like in this screenshot:
Windows 10:
Encrypting external drives is only available with BitLocker, a feature that is only included in Windows 10 Professional or better. To check that your external disk is encrypted, press the Windows key, type “BitLocker Drive Encryption” and open the “BitLocker Drive Encryption” app. The external hard disk should be marked with the words “BitLocker on.” Here is a screenshot of someone who has not yet encrypted the C: partition:
Data Pruning
Remove Old Data
It is wise to remove unnecessary data that is no longer useful or expired. This could be old backups or files or past newsletters saved on Mailchimp.

Google Yourself
Google your name and email address at least monthly.
- If you find anything that could compromise your safety, immediately ask whoever put the information online to remove it.
- After it is deleted or changed to remove your identity, remove it from Google’s cache
Tighten Security on Social Media Accounts
Whether it is personal or ministry related, go through the security settings on your social media accounts. Make sure you do not have compromising posts or pictures. Is it set to private? Make sure third party apps do not have more access than they should.
Compartmentalize Work and Personal Environments
This is probably the most challenging to implement for most. However, if you do it from the beginning, it will be easier.
Utilize separate browsers for work and personal life. Within those browsers, use independent password manager accounts. This way, your website search history, and bookmarks are separated.
Create a Risk Assessment and Contingency Plan
When working in high-risk areas, Risk Assessment and Contingency Planning (RACP) documents are designed to help you identify any potential security threats that may occur in your M2DMM context and create an appropriate response plan should they occur.
You can agree as a team how will you share about your involvement with the work, how you will communicate electronically and guidelines for team trust.
Prayerfully list out possible threats, the risk-level of the threat, tripwires and how to prevent or deal with the threat.
Schedule a Recurring Security Audit
One final recommendation is that your M2DMM team consider scheduling a recurring security audit. Apply these best practices as well as ones you learned after doing a field risk management assessment and plan. Make sure each person completes a checklist for optimal security.